
Harness CI now supports GitHub Actions, allowing users to leverage over 10k pre-built actions from the GitHub marketplace in their CI pipelines. This integration simplifies task automation, from code cloning to vulnerability scanning, enhancing the efficiency and flexibility of CI workflows.
In this article, we will learn about GitHub Actions support in Harness CI and how plugin extensibility helped templatizing action as a plugin step.
GitHub Actions let you create custom actions that can perform predefined tasks. These predefined tasks range from cloning a codebase to building a Docker image and security scanning images. Previously-created actions are present on the GitHub marketplace, with a rich support of over 10k actions.
Harness CI has added support for running GitHub Actions. This addition means that GitHub Actions can be used via the plugin step in a CI pipeline.
Usage
GitHub Actions YAML contains three attributes:
- name: Refers to the GitHub repository of the action along with the branch or tag.
- with: A map with a key and value as string. These are action inputs.
- env: Environment variables passed to the action.
You must copy with, uses, and env attributes in the plugin step settings to use a GitHub action as a plugin in Harness CI. You must also run the step in privileged mode since the GitHub action plugin uses Docker in Docker (dind).
The following is a side-by-side comparison of action YAML in GitHub actions vs. Harness CI:

The following are some examples for using actions in Harness CI.
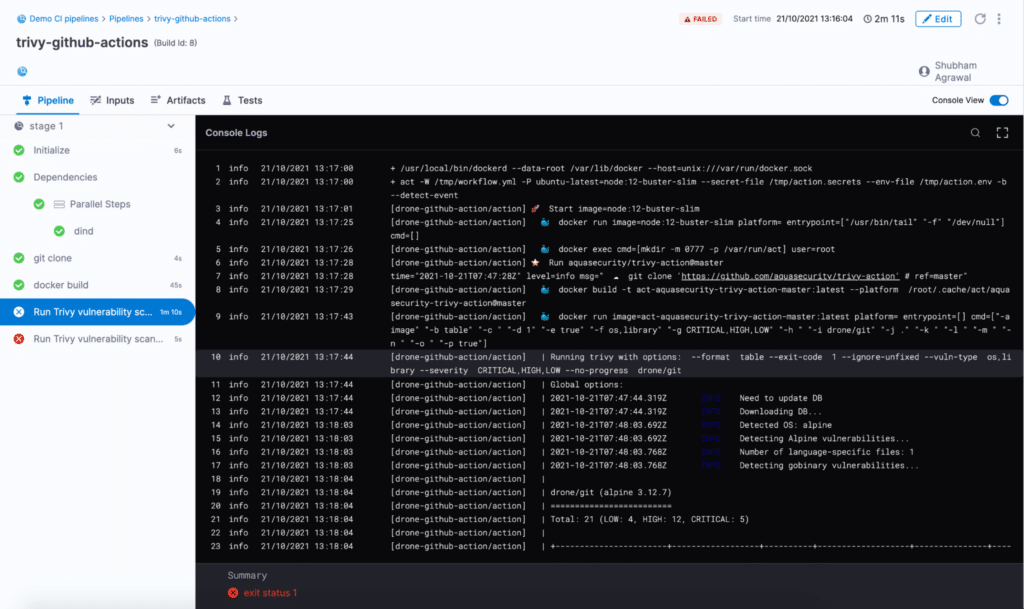
Trivy Scanning Action
Trivy is an open-source scanner for detecting vulnerabilities in container images, git repositories, and much more.
The following example scans “drone/git” container image using trivy in Harness CI.
- step:
identifier: trivy
name: Run Trivy vulnerability scanner
type: Plugin
spec:
connectorRef: dockerhub
image: plugins/github-actions
privileged: true
settings:
uses: aquasecurity/trivy-action@master
with:
image-ref: drone/git
format: table
exit-code: "1"
ignore-unfixed: "true"
vuln-type: os,library
severity: CRITICAL,HIGH,LOW
env:
CI: true
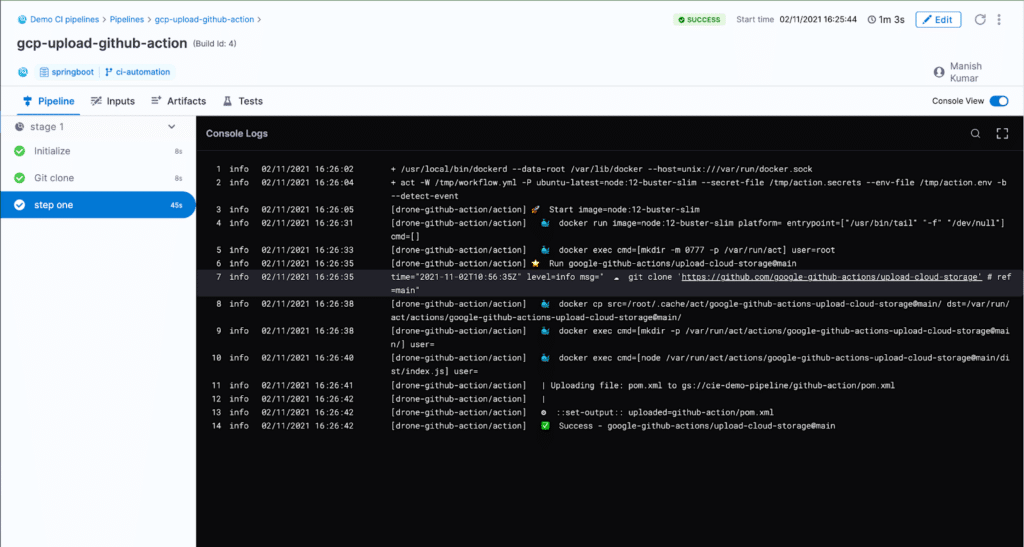
GCS Upload Action
The GCS upload action can be used to upload a file to Google Cloud storage.
- step:
identifier: gcs-uploader
name: upload file to GCS
type: Plugin
spec:
connectorRef: dockerhub
image: plugins/github-actions
privileged: true
settings:
uses: google-github-actions/upload-cloud-storage@main
with:
path: '/path/to/file'
destination: demo/gcs
credentials:
Git Checkout Action
The Git checkout action is used for cloning the GitHub repository codebase. This action can be used to clone one or more git repositories in a single stage in Harness CI.
The following example clones the primary repository present in the trigger payload. It is required to specify GITHUB_TOKEN as an environment variable to the step for cloning private repositories.
- step:
identifier: checkout
name: checkout GitHub action
type: Plugin
spec:
connectorRef: dockerhub
image: plugins/github-actions
privileged: true
settings:
uses: actions/checkout@v2
with:
ref: ${{ GitHub.event.pull_request.head.sha }}
event_payload: <+ trigger.eventPayload>
envVariables:
GITHUB_TOKEN: <+secrets.getValue("token")>

You must specify the repository name in the plugin step settings to clone a second repository.
- step:
identifier: checkout-repo-by-name
name: checkout GitHub repository by name
type: Plugin
spec:
connectorRef: dockerhub
image: plugins/github-actions
privileged: true
settings:
uses: actions/checkout@v2
with:
repository: my-org/my-private-tools
path: my-tools
ref: ${{ GitHub.event.pull_request.head.sha }}
event_payload: <+ trigger.eventPayload>
envVariables:
GITHUB_TOKEN: <+secrets.getValue("token")>
Implementation
GitHub Actions works by cloning the repository specified in the `uses` attribute and executing the steps present in the `action.yml` file from the cloned action code.
The CI plugin for GitHub action uses nektos/act, which is an open-source project to execute GitHub Actions locally. Nektos/act runs a Docker container on which the GitHub action workflow is executed. The CI plugin creates a workflow for the input action step, and then executes it via nektos/act. The following is the link for the plugin source code: Plugin Source Code
Conclusion
We have shown that the extensibility and simplicity of plugins in Harness CI enabled the addition of many actions with just a single plugin. This demonstrates just how pluggable Harness CI can be. I hope you try your favorite action in Harness CI, and possibly create your own plugin for your custom-tailored tasks.
For further reading on Harness CI, why not take a gander at our Migrating From Jenkins to Harness CIE piece?
Checkout comparisons: Harness v.s. GitHub Actions
